Importance of Securing Business Data – Common Cybersecurity Mistakes
We get it, owning and running a business is anything but easy. You don’t have any “free” time to keep up with what’s happening in the technology world. And yet, the decisions and investments you make today will affect your business far into the future. Although there is no one-size-fits-all cybersecurity strategy for businesses, business owners need to understand that there are basic principles every organization must adhere to in order to ensure its safe from cyber attacks. Making smart technology decisions is easy—if you are aware of the common cybersecurity mistakes to avoid. While each business and start-up face different technology needs, the following list applies to almost any business:
- Not backing up your data
- Your business plan doesn’t include an IT plan
- Cybersecurity through obscurity = Bad strategy
- Doing it yourself vs. investing in good IT support
- Not proactively refreshing your technology
- Not ensuring your hardware and software are compatible
- Failing to maintain your IT systems
- Thinking that all hardware is created equally
- Failing to adequately train your staff
1. Not Backing up Your Data
It’s impossible to stress this enough. Just like you have an insurance policy to protect your home, auto, and personal belongings from loss or damage, you need a similar insurance policy for your business data. Imagine what would happen to your business if you lost your critical files, financial information, or customer data? What would it cost you to recover from such an incident—not just in terms of money, but also in lost time, lost customers and damaged reputation?
Two very important things to know here. Always make regular computer backups and always test those backups to ensure you can restore files. The easiest and most pain-free way to do this is with encrypted backup software, such as eSilo, that automatically backups up your files, securely stores multiple copies offsite or in the cloud, and enables one-click restore of any file or folder.
2. Your Business Plan Doesn’t Include an IT Plan
Create a roadmap for your technology (IT strategy) needs that you will review annually (or sooner depending on business growth). When budgeting for technology, be sure to consider the total cost of ownership (TCO), not just the purchase price of the hardware, software, or services you buy. TCO includes expenses for software upgrades, hardware maintenance, technical support whether a person or hourly, as well as additional costs for licenses, renewals, subscription fees etc.
One major consideration is what you will do in the event your technology is offline or unavailable. How will you continue to run your business? The robustness of your technology infrastructure should be a core focus of your Business Continuity and Disaster Recovery Plan.
3. Cybersecurity Through Obscurity is Always a Bad Strategy
Some small business owners believe that because of their size they have a lower risk of being targeted by cyber thieves. This couldn’t be further from the truth. According to multiple studies, just shy of 50% of cyber attacks last year targeted small businesses (Small Businesses Beware: Half of all Cyber-Attacks Target You ), in large part because small business owners pay ransoms, have valuable data, and are easier to hack because they often make the most common cybersecurity mistake – they don’t invest in adequate cyber-defenses.
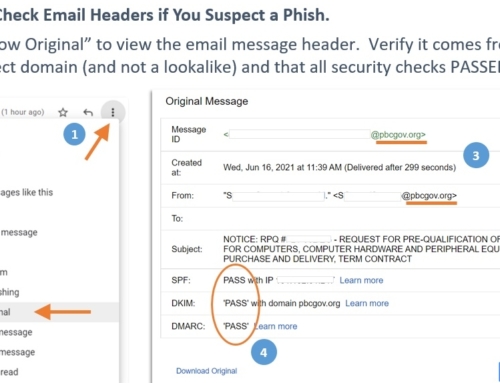
For these reasons, the cybersecurity of computers and files should be every business owner’s top IT concern. Online viruses, phishing scams and ransomware are more abundant than ever, and businesses need to adopt a layered cybersecurity defense. On your computers and servers, ensure all software remains up-to-date by allowing automatic software updates. Never postpone critical updates or security patches for more than 24 hours, and make sure you have an anti-virus program running on all your devices.
On your network, make sure your internet and WiFi connections are encrypted and secured. If you have a firewall, make sure your IT support has blocked all unnecessary incoming traffic.
Users must also take measures to protect their passwords. Best practices include changing passwords regularly, using unique passwords for every site, and never writing passwords down or sharing them with co-workers.
PRO-Tip – use complex phrases, avoid the most commonly used passwords (Top Passwords Leaked in Data Breaches), and anything easily guessed (e.g. family member names, birth dates, etc.). If you find it difficult to keep all your passwords straight, then invest in a password manager app for a few dollars a month.
4. Doing-It-Yourself Vs. Investing in IT Support
Most modern businesses would grind to a halt without working computers, software, internet, and access to your data files. As a busy business owner, you can’t afford to DIY troubleshoot the inevitable computer crash or network disruption – it’s another common cybersecurity mistake. This is where it pays to have a trusted, experienced IT support technician on call who can get you back up and running in no time.
It’s not easy to find a good and reliable technician. Look for updated training, certifications and references to contact when sourcing your support. You’ll want someone who has experience with the technology tools you use, and who is bonded and insured, and willing to sign confidentiality and non-disclosure agreements to protect your privacy.
5. Not Proactively Refreshing Your Technology
Don’t turn your technology into a dust museum. Look at proactively refreshing your servers and PCs every 3-5 years to minimize unplanned (and inevitable) hardware failures that will catch you by surprise.
This refresh cycle is a general guideline. Your business needs may require you to refresh earlier or later depending on how your technology is used, and the minimum system requirements of the software you are using.
6. Not Ensuring Your Hardware and Software is Compatible
Imagine you just downloaded the latest and greatest software or operating system upgrade but forgot to check whether your hardware can support the new processing load and memory requirements of the new software … and now it doesn’t work. Oops! Best to check in advance that your server is up to date and capable of supporting your new upgrade. Newer versions of software typically need more computing resources to function properly. Specifically, be sure to check the minimum requirements for the computer’s processing speed (CPU), memory (RAM), and storage capabilities.
PRO-Tip – To avoid this common cybersecurity mistake, always go a factor of 1-2 times over and above the minimum requirements when matching equipment to software. You will have just extended the usability of the equipment to account for future upgrades.
7. Failing to Maintain Your IT Systems
Once everything is installed and running, your days of maintenance have just begun. Schedule regular checks by your trusted IT support, at specific intervals. Servers and the software on them require more care than simply checking the cabling or PC hardware.
Server backup systems on the other hand, require more maintenance than other systems to ensure smooth-running. This is another reason to consider using a full-service data backup company like eSilo to execute, maintain and test your backups so you know they are being done correctly.
8. Thinking All Hardware is Created Equal
That router you buy for your home and the one needed for your business really are different. Cutting corners by purchasing cheap, consumer-grade equipment will lead to headaches in the long-run, including increased downtime, slower and lower quality data communications, less sophisticated cybersecurity protections, and in general lead to more frequent issues and shorter equipment life. Simply put, always purchase business-class hardware for all mission-critical applications.
9. Failing to Adequately Train Your Staff.
Too often I have seen companies deploy expensive software solutions expecting them to increase productivity, only to find the exact opposite has happened. This is because their staff was not properly trained on the new system, and old business practices were never revised to eliminate manual steps now addressed with the new software.
When implementing any kind of change, you cannot forget the human element and the importance of training your staff in cybersecurity. Ways to do this easily include group training session(s) that include hands-on practice or demos, or a more streamlined approach where one staff member is the designated trainer for the rest of the team.
While there are plenty of other common cybersecurity mistakes to avoid that we could add to this list, these are the most frequent issues we’ve seen over our 20 years of working with small and medium-sized businesses across the US.
If you’ve got more to add or have any feedback to offer, please comment below or email our team at: info@esilo.com.
Interested in a complimentary IT strategy consultation with our CEO, Cathy Miron? Contact us to book a session today 561-747-6880.