Cyberattacks are on the rise. Hackers target victims every day. As a result, even highly protected, large-scale businesses are vulnerable. In 2021, Kaseya, a global IT company, was hit by a cyberattack that affected 1,500 businesses, shut down Swedish supermarkets, and caused local governments to fail. Cybercriminals and their damages are growing dramatically in number and frequency.
Kaseya has since recovered from the attack, but an unprotected business can be completely wiped out by a cyberattack. Damage repair can cost thousands of dollars. Not to mention the several days to months of downtime used to rebuild from the ground up. The time has come to implement cybersecurity efforts in businesses large and small.
Table of Contents
What should be in my Weapons Vault?
1. Antivirus Software
A computer virus can easily infiltrate your network and cause irreversible damage if proper defenses are not in place. Viruses are strategically disguised in emails, URLs, and Word documents. Safety Detectives found 38% of malware camouflaged as a Word document. Fortunately, good anti-virus software is programmed to scan incoming files like Word documents and/or code on your device speedily. Then, it will detect and remove any viruses during routine scans. Without these features, the effectiveness of the antivirus software is minimal and a waste of money.
2. Backup Solution
A flat tire is a frustrating experience, but a spare can alleviate that. Likewise, a backup solution acts as a spare during cyberattacks. A backup solution will encrypt files to be unreadable to outside parties, create copies of data, and restore lost or corrupted files. These features empower your business to bounce back after an attack. But without a backup solution or the use of a free service, the future of your business is uncertain. A study found that 93% of companies filed for bankruptcy a year after data loss. If the companies had a backup solution to recover or obtain a copy of their data, they would likely be standing strong today. Data loss is a ticking time bomb, and free, unreliable backup solutions like Google Drive add fuel to the fire. However, the features of a good backup solution can readily diffuse it.
3. Multi-Factor Authentication
Multi-factor authentication, or MFA, can stop a hacker from impersonating you. MFA requires multiple factors to prove one’s identity to a website, which is usually a combination of something the user knows like a password, and something the user has which is a code. Codes are generated randomly and created or sent through a few methods. Most websites send their MFA codes through email or SMS text message, but, the better websites support the use of an Authenticator app on your mobile device. This is because an attacker can steal MFA codes more easily from email or text messages if they have access to your inbox or installed malware on your phone. Whereas, authenticator apps generate a unique MFA code every 60 seconds, making codes difficult to steal.
4. Strong Passwords
People love convenience, and their passwords are too. Convenient passwords are weak passwords that put your business or personal data at risk. Unsettlingly, 80% of data breaches are because of weak passwords. Moreover, passwords are frequently reused and recycled. One password can access a majority, if not all, personal and work accounts. Data port found 51% of people have the same passwords for all their accounts. A hacker can retrieve one password and use it to also breach business data. To counteract, utilize a lengthy and strong password that contains a jumble of letters & symbols. On the contrary, weak passwords are easy to guess because they’re few characters in length and contain personal information. Passwords are one of the first layers of protection, so use a strong over a weak password.
5. Password Manager
People regularly forget passwords. As a result, new passwords are often variations of ones previously used. According to CNET, the average person has to remember more than 85 passwords for all of their online accounts. The easiest way to keep track is to get them out of your head and into a password manager. A password manager is like a safety deposit box because your long, unique, and complex passwords are secured in a digital vault. No more guessing passwords or constantly resetting your login credentials. An additional feature that businesses will love is the ability to securely share log-in credentials with their co-workers. Additionally, security features such as central policy management, audit logs, and the ability to force-reset a user’s Master Password (which controls access to their password vault) are critical to a growing business. The features listed are often features of paid plans. So, invest in a password manager rather than settling for a free one, which has less security and features.
6. Cybersecurity Awareness Training
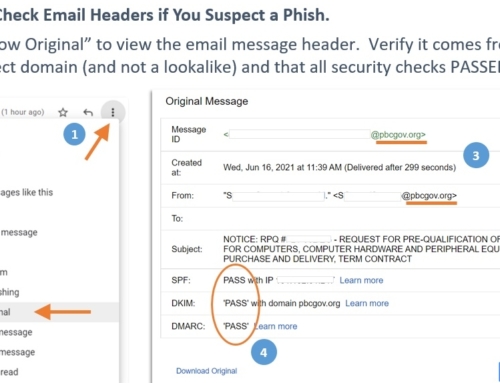
Knowledge is power, and cybersecurity awareness training is a powerful security measure. It’s paramount that employees receive awareness training. The reason is, a majority of your employees might know to be cautious of phishing emails, but does the new recruit? The new employee could fall for a phishing email that gives a virus access to the network. According to ABC News, malicious emails have increased an alarming 600%. Awareness training will help your employees identify and stop an attack like a phishing email. Without awareness training, your employees are left stabbing in the dark. They could easily fall for hackers’ schemes and cause damage to your business.
7. Understand Hacker Psychology
Bruce Schneier, a Cryptographer & Harvard University Lecturer, said “Amateurs hack systems, professionals hack people”. Hackers know code inside and out, but they also know human psychology like the back of their hands. To have the upper hand, understand the psychology of hackers.
Hackers are opportunists and will do anything for money. They will ruthlessly destroy your business, blackmail, and more till they receive their desired outcome. Hackers move from business to business to hunt for vulnerabilities to get their foot in.
Once they’re in, a hacker can launch a successful attack. Any vulnerability is an opportunity for hackers like it’s a big dollar sign. Luckily, the cyber defenses listed can lessen vulnerabilities and reduce the number of attacks. Understanding hacker psychology helps to know what a hacker looks for and what their schemes look like, so you can avoid their minefields.
The sobering fact is, your business is always on the battlefield. However, the weapons listed will enact lines of defense to reduce vulnerabilities. As a result, your business can bounce back as if nothing happened, soften the blow, or prevent a disaster altogether. Prepare for cyber warfare by building up your arsenal of defenses and stocking up your weapons vault, and your business can flourish no matter the circumstance.